Security MobilITy
Defend from Anywhere
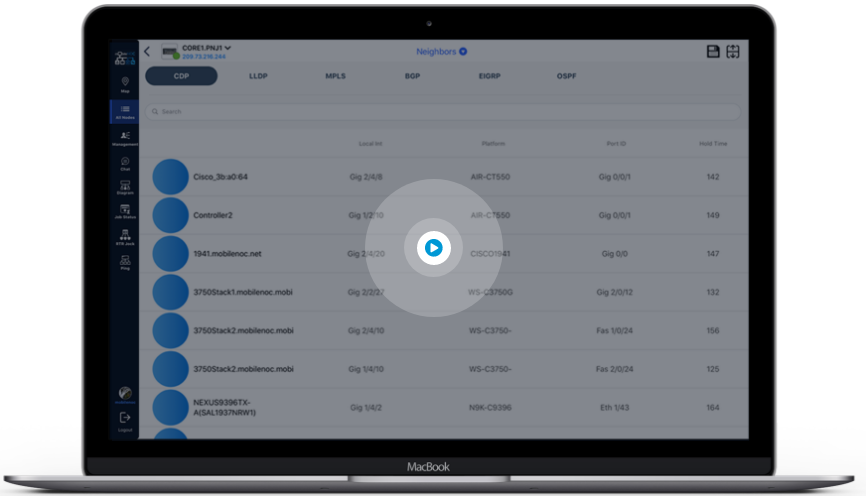
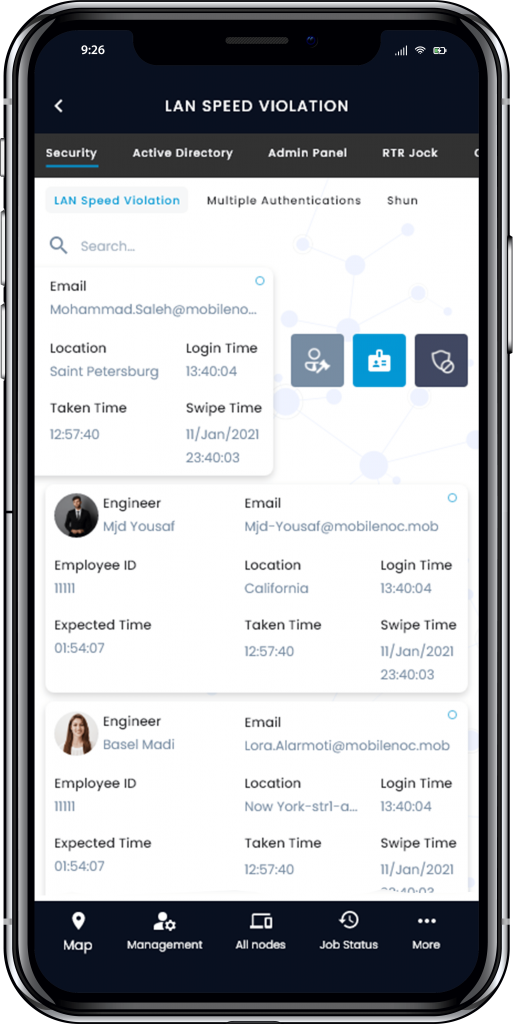
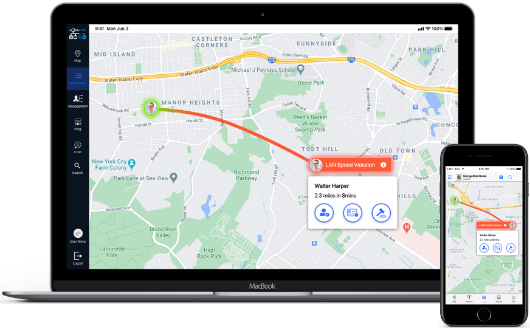
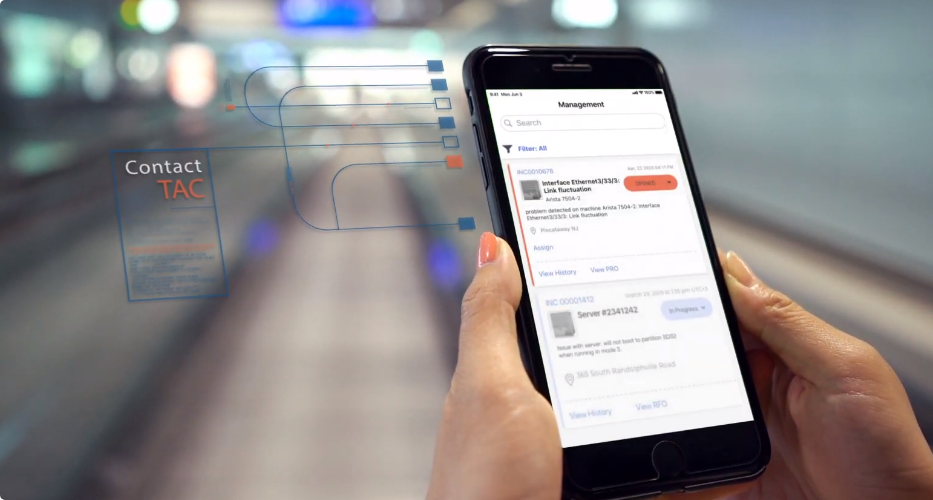
Security MobilITy provides a single API for all network management, operations, and automation while leveraging the power of mobile devices. This revolutionary platform empowers security teams to monitor and prevent potential events from a smartphone, tablet, or smartwatch.

Are you completing security and compliance tasks manually? Use our ZeroCode Automation for:
- Threat detection & response. Automate threat analysis, investigation, response, containment, and resolution.
- Compliance & audit. Automate security and compliance processes, apply best practices and policies. Deploy VTY ACLs, hardening, SNMP, AAA, and Syslog template configurations.
- Operations compliance. Automate critical tasks, such as device configuration backups, verifying boot statements match OS, and code/firmware upgrades